From Seed to Series B: How Your IT and Security Posture Must Evolve at Each Funding Stage

Modern SaaS and tech-enabled startups don’t just sell software anymore—they sell reliability, safety, and trust.
Your biggest customers and your investors are increasingly asking the same questions:
- Can we rely on you to stay online?
- Can we trust you with our data?
- Are you building a company that can scale without falling apart?
Those questions show up as security questionnaires, due-diligence checklists, and “quick” follow-up emails from procurement or investors. At Pre-Seed, the bar is relatively low: don’t be reckless. By Series B, the bar is much higher: show us formal controls, a track record of following them, and evidence.
This article walks through how expectations evolve from Pre-Seed to Series B, what you actually need to put in place at each stage, and how to avoid nasty surprises during technical due diligence. The idea is not to scare you into building a bank-grade security program on day one, but to give you a realistic, staged roadmap that fits how startups really grow.

Pre-Seed (0–10 People): Don’t Be Reckless
At Pre-Seed, you’re trying to answer basic questions: does this product make sense, and will anyone use it? No investor expects a full SOC 2 program at this point. What they do expect, however, is that you’re not being careless with your customers’ data or your own IP.
What investors and customers quietly expect
If you talk to an angel investor who’s seen a few startups implode, they’ll rarely ask you for policies. They will, though, probe for signs of chaos: “If your lead engineer disappeared tomorrow, could anyone else deploy or fix things? If your database crashed, could you restore it?”
Under the hood, what they’re really looking for is basic hygiene:
- You’re not sharing a single Gmail login between founders.
- You’ve turned on multi-factor authentication (MFA) for the truly critical stuff: your cloud platform, your code repository, and any production admin console.
- You’ve enabled backups for your production database and your code is safely in a hosted repository, not just on someone’s laptop.
- Your laptops are encrypted and not left lying around unlocked.
No one expects a thick security manual, but they do expect that systems aren’t living entirely in one person’s head. A simple wiki page with “Here’s where production runs, here are the main tools we use, here’s who has the keys” goes a long way.
What to put in place at this stage
Think of Pre-Seed IT and security as “don’t lose the company over something stupid.”
Access Control
Start with a team-wide password manager and require MFA for your most sensitive accounts. Avoid sharing passwords over Slack or keeping them in a spreadsheet. If an account really must be shared for now, store it in the password manager.
Backups
Turn on whatever managed backups your cloud or database provider offers, and then do at least one trial restore into a test environment. The goal isn’t perfection; it’s simply to know you can recover if someone accidentally drops a table.
Documentation
One or two wiki pages are enough. List your core systems and owners, sketch a very rough architecture (“frontend here, API here, database here”), and note who to contact if something breaks. This is about resilience, not compliance.
Asset Security
Finally, make sure all company laptops use full-disk encryption (modern operating systems have this built in) and basic endpoint protection. Even a relatively simple consumer-grade solution is fine at this stage.
The Pre-Seed “must haves” in plain terms
By the time you’re closing a Pre-Seed round, you should be able to say, without hand-waving:
- “We use a password manager for company accounts, and MFA is enabled on our cloud, code repo, and production admin tools.”
- “Our production database is backed up automatically, and we’ve successfully tested restoring from a backup.”
- “All company laptops are encrypted and protected with strong login credentials.”
- “We have a simple internal page that documents our main systems and who manages them.”
- “When someone joins or leaves, we have a short checklist we follow to add or remove their access.”
That’s it. You don’t need more than that at this stage, and trying to do a full-blown compliance project this early is overkill.

Seed (10–40 People): Basic Hygiene and Repeatability
At Seed, you start to feel growing pains. You’re hiring quickly, you’re handling more data, and suddenly a prospect sends you a 40-question security questionnaire. That’s usually the moment founders realize, “We need to get our house a bit more in order.”
How expectations change at Seed
Seed investors and early enterprise or mid-market customers still don’t expect a mature compliance regime, but they do expect reproducible processes instead of heroics.
They’ll ask to see a security policy or an acceptable use policy for employees. They’ll want to know that every laptop is managed, not just “most of them.” They may ask, “How do you onboard and offboard employees?” and “How often do you back up data?” Some may ask whether you have plans to pursue SOC 2, simply to validate that you’re thinking ahead.
In practice, the bar here is: you’ve moved from “everyone does what seems right” to “we do things in a consistent way, and we’ve written down what that way is.”
Concrete steps to take at seed
Access Control
Access control is the first big area to professionalize. This is typically when you introduce single sign-on (SSO) for at least your core apps—cloud infrastructure, code hosting, project management, and any tool holding customer data. MFA should now be standard for all users, not just engineers or admins.
On-boarding / Off-boarding
It’s also time to formalize your joiner/mover/leaver process. When someone joins, they should get a predictable set of tools based on their role. When they change roles, someone should review whether their access needs to change. When they leave, there should be a checklist: remove SSO access, revoke access to key systems, reclaim or remotely wipe their laptop.
Backups
Backups move from “we turned them on” to “we know how they work.” Define what you actually back up, how often, and how long you retain data. For your production database, daily backups are usually a baseline; for highly transactional systems, you may want more frequent snapshots. Schedule regular test restores—quarterly is a reasonable starting point—and keep a short record of each test.
Documentation
Documentation starts to look more like a small, coherent set of policies. These don’t have to be 30-page documents. A few concise policies—information security, access control, device/acceptable use, and a simple incident response procedure—are usually enough. These should live in a place everyone can access (your internal wiki) and be written in plain language.
Asset Inventory
This is also a good time to establish an asset inventory. For now, a spreadsheet is fine: list your laptops, who uses them, and your core SaaS systems and their owners. Pair this with basic mobile device management (MDM) so laptops are encrypted, kept up to date, and can be remotely locked or wiped if needed.
Logging & Alerts
Finally, set up centralized logging and basic alerting for your production environment. Most cloud providers make it fairly simple to pipe logs into a central place. At Seed, it’s usually enough to have error and uptime alerts going to Slack or email, and a simple incident response “playbook” describing who gets paged and how you communicate during an outage.
What you should be able to demonstrate by the end of Seed
By the time you’re raising a Seed round or closing your first meaningful B2B deals, you want to be able to show:
- Most of your important apps are behind SSO, with MFA required for everyone.
- You have a defined, written process for onboarding and offboarding employees, and you actually use it.
- Your production databases are backed up daily (or better), and you’ve successfully tested restoring them and kept a record of that test.
- There is a short, readable policy set covering security basics and how employees are expected to use company devices and systems.
- You maintain an up-to-date list of devices and key systems.
- Production logs are centralized, and there are simple alerts and an incident response procedure in place.
- You’ve at least thought about SOC 2 or similar frameworks and have a rough idea of when you might need them.
None of this should feel like heavy bureaucracy. The goal is to avoid relying on tribal knowledge and to show that you’re operating intentionally, not by accident.

Series A (40–120 People): Make Security and IT Managed Functions
Series A is usually the stage where security stops being a “best effort” side project and becomes someone’s actual job, at least part-time. The stakes are higher: you’re signing larger contracts, you’re integrating with customers’ internal systems, and investors are asking more pointed questions during technical due diligence.
How investor and customer expectations evolve
At this point, the expectation is that security and IT are no longer ad hoc. Someone owns them. The board may ask, “Who is responsible for security?” and expect a clear answer.
Larger customers will want to see more formal evidence: policies with dates and approvals, proof of regular access reviews, backup test logs, incident reports, and perhaps early steps toward SOC 2. When they ask, “How do you manage vendors?” they expect more than “We look at their website and it seems fine.”
They’re effectively asking: is this company building security and reliability into its operating system, or is it still depending on a few heroic engineers?
What to build at Series A
Access Controls
By now, SSO and MFA should be standard across almost all company tools. You should define role-based access control (RBAC) for your production environment and key admin systems. Not everyone needs admin rights; many people can operate happily with read-only or limited scopes. Schedule periodic access reviews—quarterly or twice a year—where managers confirm that their team members still need the access they have.
Backups & DR
Disaster recovery deserves a proper plan at this stage. This doesn’t have to be a huge document, but it should clearly state your recovery time objective (RTO—how quickly you expect to be back online) and recovery point objective (RPO—how much data loss you can tolerate) for each critical system. Then, test that plan. Run at least one exercise where you simulate a failure and measure how long it takes to restore, and how much data you lose, in practice.
Documentation
Your documentation should now include a more complete security and IT policy set. In addition to the Seed policies, you’ll likely add change management, vendor management, data retention, and business continuity. Keep your architecture and data flow diagrams up to date; these are invaluable in both audits and incident response. Start or maintain a simple risk register where you list your top risks, how you’re addressing them, and who owns each one.
Asset Inventory & Management
On the operations side, device management should be comprehensive: all company devices under MDM, full-disk encryption, standardized builds per role, and centrally managed endpoint protection. Your IT/helpdesk function—whether internal or managed—should be using a ticketing system to track requests, incidents, and changes. For production, changes should go through version control, code review, and your CI/CD pipeline, with records of who deployed what and when.
Cybersecurity
Security ownership becomes important here. That might be a Head of Engineering with security as a defined responsibility, a dedicated security lead, or a virtual CISO/managed provider. The important thing is that there is a named person or function accountable for your security posture, your roadmap (e.g., toward SOC 2), and your responses to incidents and questionnaires.
What you should be able to show by the end of Series A
By the time you close a Series A, it’s reasonable for investors and enterprise customers to expect that you can demonstrate:
- SSO and MFA for essentially all employees and most critical apps.
- Clear RBAC for production and admin systems, with evidence of periodic access reviews.
- A written disaster recovery plan, with specified RTO/RPO and at least one documented DR exercise.
- Centralized logging and monitoring for your application and infrastructure, with on-call processes and an incident management workflow.
- A coherent set of security and IT policies, reviewed and updated periodically.
- A complete asset inventory that’s actually maintained.
- Full device management with standardized builds and endpoint protection.
- A ticketing system that serves as the system of record for IT requests, incidents, and change management.
- A specific plan for SOC 2 (or similar) and, often, meaningful progress towards a Type I or even Type II report.
At this point, you’re not just trying to “not be insecure”; you’re demonstrating that you can run a predictable, auditable operation.

Series B (120–250 People): Operate Like a Mature, Auditable Organization
By Series B, your company often looks and feels like a “real” organization from the outside. You may be selling to enterprises, working with regulated customers, or handling sensitive data at scale. Due diligence becomes deeper: 200–300-question security questionnaires, detailed conversations with customer security teams, and formal audits.
The new bar at Series B
Investors and customers now want not just promises, but proof. When they ask, “Do you perform access reviews?” they expect to see records. When they ask about incident response, they want to know about your last real or simulated incident and what you learned.
They’re looking for a security and IT function that runs like any other core business function: clear roles, repeatable processes, documented controls, and regular measurement and improvement.
What maturity looks like at this stage
IAM
Identity and access management should be fully lifecycle-driven by Series B. New hires, role changes, and terminations trigger automated or semi-automated workflows that grant and remove access based on defined roles or groups. Managers should periodically certify their teams’ access to sensitive systems, and you should be able to show that these certifications happened.
BCDR
Your disaster recovery and business continuity planning should include regular, structured exercises. At least once a year, run a broader DR test that simulates a realistic scenario such as a regional cloud outage or a ransomware attack. Capture how long it took to recover, how well your communication plan worked, and what you’ll improve.
Documentation
Policies and procedures should be living documents. There should be a schedule for annual review, clear version history, and evidence of approval by appropriate leaders. Your architecture and data flow diagrams should reflect your current environment, including key third-party providers, and be used during design decisions and vendor assessments.
Oberservability
Monitoring and logging usually mature into a more comprehensive security monitoring capability—sometimes a security information and event management (SIEM) system or a managed detection and response service. The important thing is not the specific tool, but that you can detect and respond to suspicious activity, not just outages. Incident response should be practiced, with roles defined (who leads, who communicates, who handles forensics) and post-incident reviews feeding back into improvements.
Compliance & Certification
On the compliance side, many B2B SaaS companies at Series B either have a SOC 2 Type II report in hand or are far along in the process. Others may move toward ISO 27001, especially if they sell globally. A basic privacy program should be in place, including data mapping, data processing agreements, and, where required, DPIAs and potentially a designated privacy lead. Vendor risk management should be formal enough that you can demonstrate how you evaluate, onboard, and periodically review critical third-party vendors.
Training
Training and culture matter more at this stage. Security training should be part of onboarding, refreshed regularly, and tracked. Engineers and administrators should receive more specialized training on secure coding, infrastructure hardening, and secrets management.
What you should confidently demonstrate by the end of Series B
By Series B, it’s reasonable to expect that you can show:
- Automated or well-orchestrated identity lifecycle management and regular access certifications for critical systems.
- A disaster recovery and business continuity plan that has been tested recently with full-scope exercises.
- A policy and procedure library that is up to date, versioned, and regularly reviewed.
- Centralized security monitoring and an incident response process that has been exercised and refined.
- A completed or in-progress SOC 2 Type II (or equivalent) with a clear timeline, especially for enterprise-facing SaaS.
- A structured vendor risk management program with assessments of your key vendors.
- A company-wide security training program with evidence of participation.
- A documented risk register and at least annual risk assessments that feed into your roadmap.
At this point, your goal is to look—and to operate—like an organization that enterprises and investors can trust at scale.
Common Pitfalls That Slow Down Deals and Fundraising
Across all these stages, certain recurring patterns cause problems during fundraising or enterprise sales.
Sloppy Offboarding
It’s surprisingly common for startups to discover that ex-employees still have access to email, GitHub, or production systems weeks after leaving. When this comes up during due diligence, it immediately undermines trust.
“Schrödinger’s Backup”
The data is backed up… probably. No one has ever tried to restore it. When auditors or customer security teams ask for evidence of restore tests, and you can’t produce any, it’s a major red flag. In real incidents, it can be catastrophic.
Absence of any Asset Inventory
If you don’t know what devices you have, where they are, or whether they’re encrypted, it’s almost impossible to respond confidently to a lost laptop or suspected compromise. It also makes it hard to convince outsiders that your controls apply to “all endpoints.”
Unmanaged or Unencrypted Laptops
For a small, early-stage team, this might feel minor. To an enterprise customer, a lost unencrypted laptop with access to production or sensitive data can be a reportable data breach.
Access Controls
Shared admin accounts, a lack of role separation, and no access reviews are repeatedly flagged in security questionnaires. They suggest an environment where it would be hard to investigate or contain an incident.
Certifications
Finally, many SaaS founders under-estimate how often they’ll be asked about SOC 2 or equivalent frameworks. It’s not true that “no one will buy from you without SOC 2,” but it is true that for many mid-market and enterprise deals, not having a clear plan or progress toward SOC 2 will slow you down, or push you behind a more mature competitor.
On the flip side, one anti-pattern is trying to do everything far too early—trying to become ISO 27001-certified at Pre-Seed, for example. That kind of premature optimization eats focus and budget that should be going into finding product-market fit. The art is in doing just enough at each stage to be safe and credible, without drowning in process.
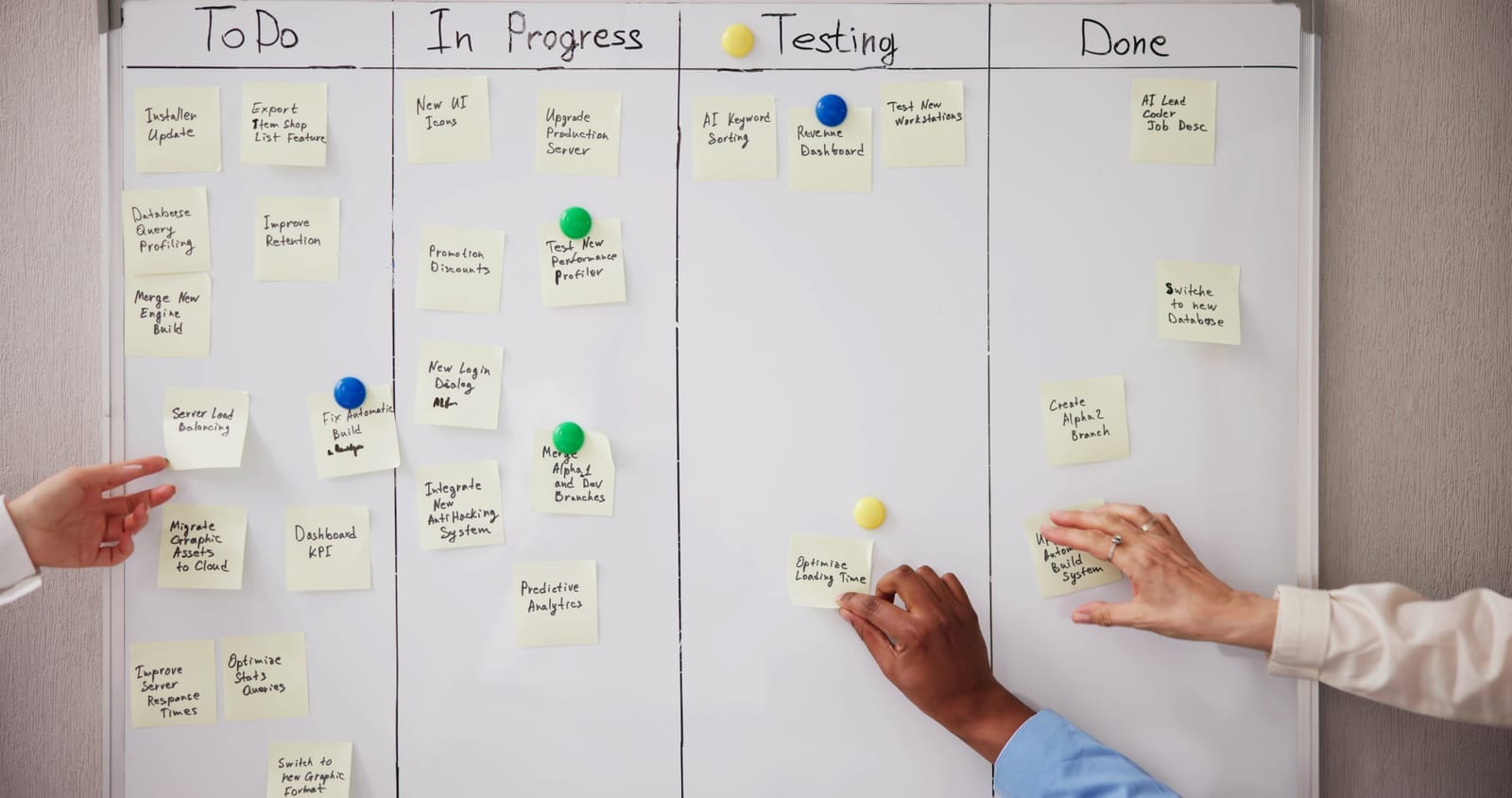
A Simple, Staged Roadmap
Putting all of this together, you can think of your roadmap in four steps.
- At Pre-Seed, focus on not being reckless. Use a password manager and MFA for critical systems, turn on backups and test them once, encrypt laptops, and write down the basics of your environment and access process.
- By Seed, layer in repeatability. Introduce SSO for core tools, formalize onboarding and offboarding, define simple policies, centralize logging and alerts for production, maintain an asset inventory, and start planning for SOC 2 if you’re selling B2B.
- By Series A, treat security and IT as managed functions. Expand SSO coverage, define RBAC and do access reviews, write and maintain a DR plan with exercises, standardize devices under MDM, use a ticketing system for IT and changes, assign a clear security owner, and make real progress toward SOC 2.
- By Series B, operate in a way that’s auditable and defensible. Automate identity lifecycle management, run full DR and business continuity tests, maintain a complete and reviewed policy library, implement mature security monitoring and incident response, complete or be close to completing SOC 2 Type II (or equivalent), formalize vendor risk management, and embed security training and risk management into your culture.
Making It Practical (and Affordable)
For many startups, all of this can sound daunting—especially if you don’t have in-house IT or security leadership. In practice, you don’t need to hire a large team overnight.
Many growing companies partner with managed IT and digital transformation providers that specialize in cloud-first, secure setups and flexible, OPEX-based models. The key is to choose partners that are vendor-agnostic and “fee-only,” so recommendations are made in your best interest rather than to push specific products. A good partner can handle day-to-day IT operations, device management, and basic security monitoring, while a fractional security leader (or vCISO) helps design your roadmap and prepares you for SOC 2 or similar audits.
The most important thing is sequencing. You don’t need Series B controls at Pre-Seed, but you also don’t want to be bolting on basic hygiene the night before your Series A diligence call. If you align your IT and security posture with your funding stage, you’ll not only reduce risk — you’ll also close deals faster and make your company much easier to invest in.